Step 01
Step 02
ICS Security Advisories
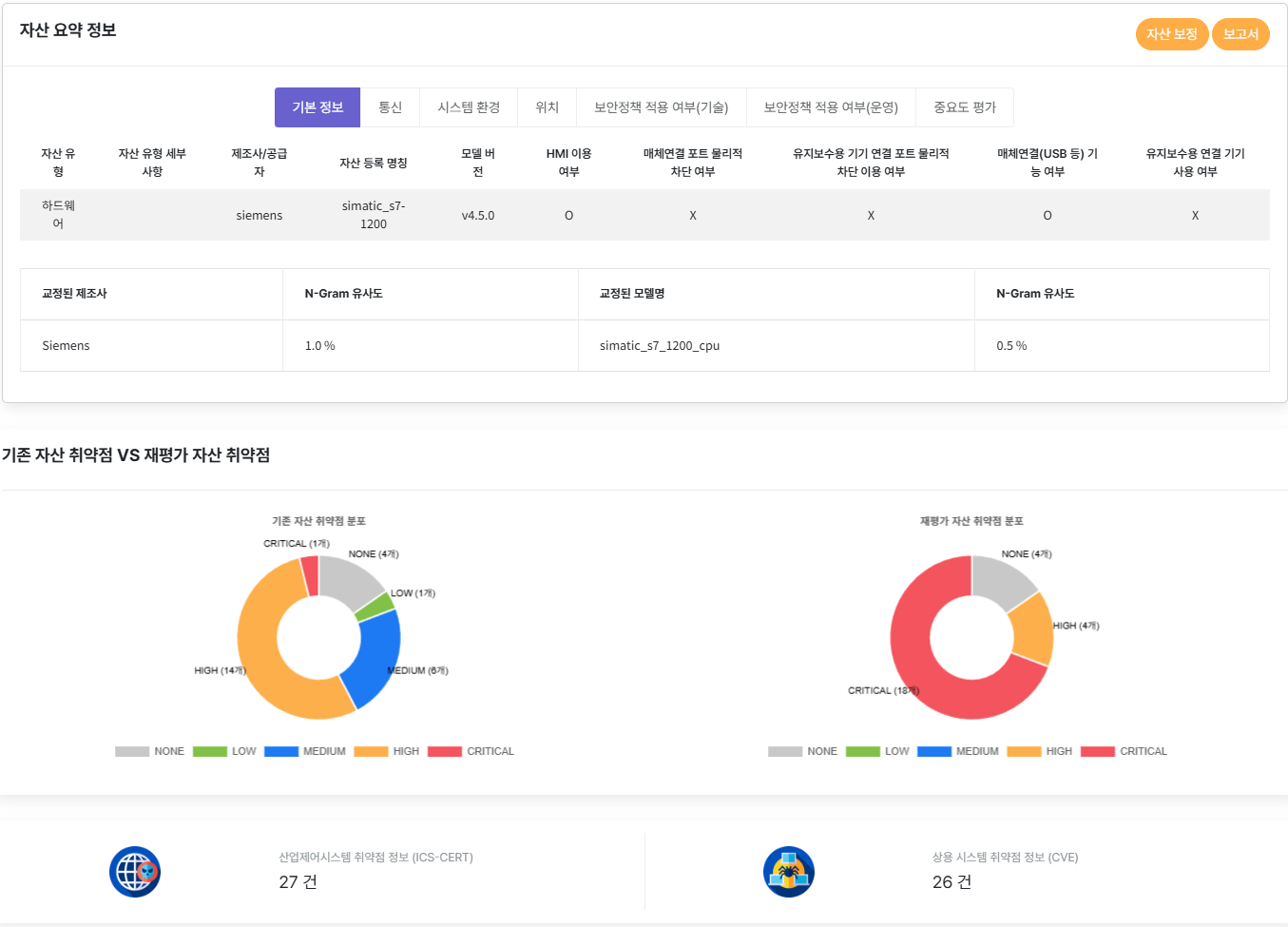
Step 03
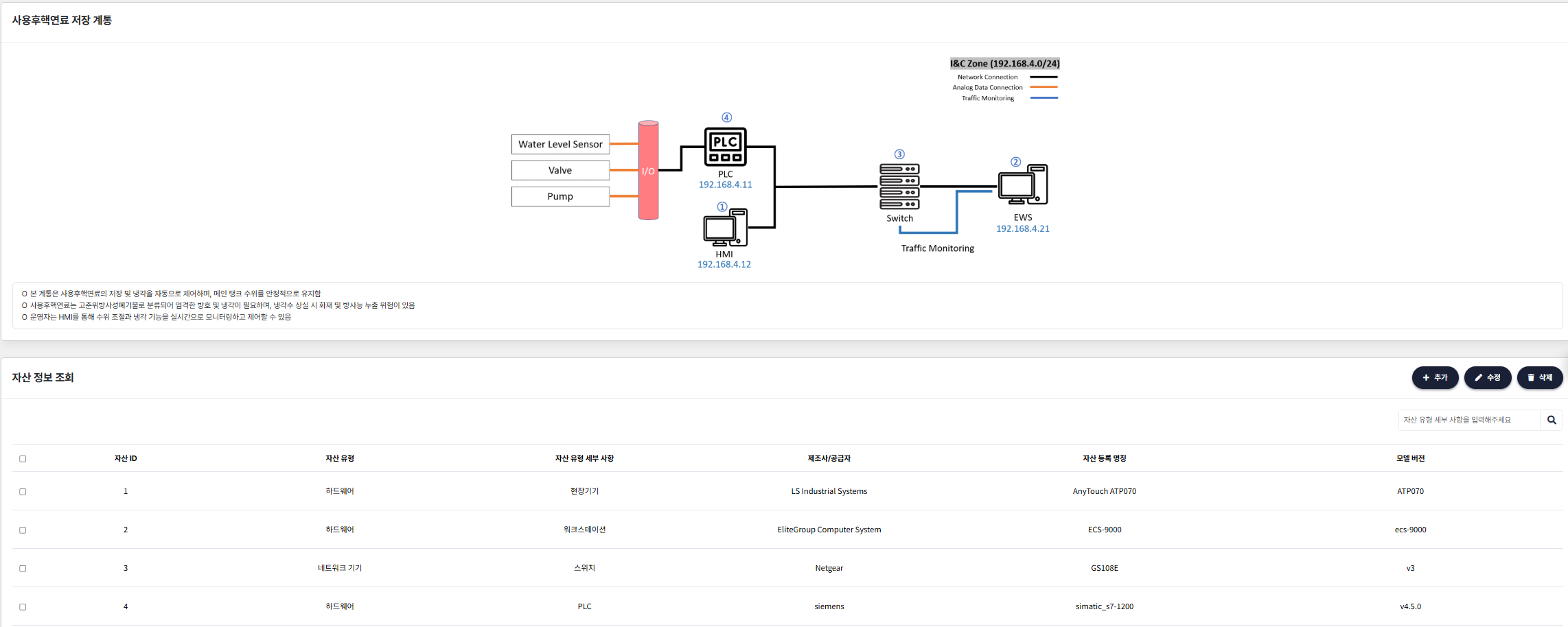
System Information Lookup
Step 04
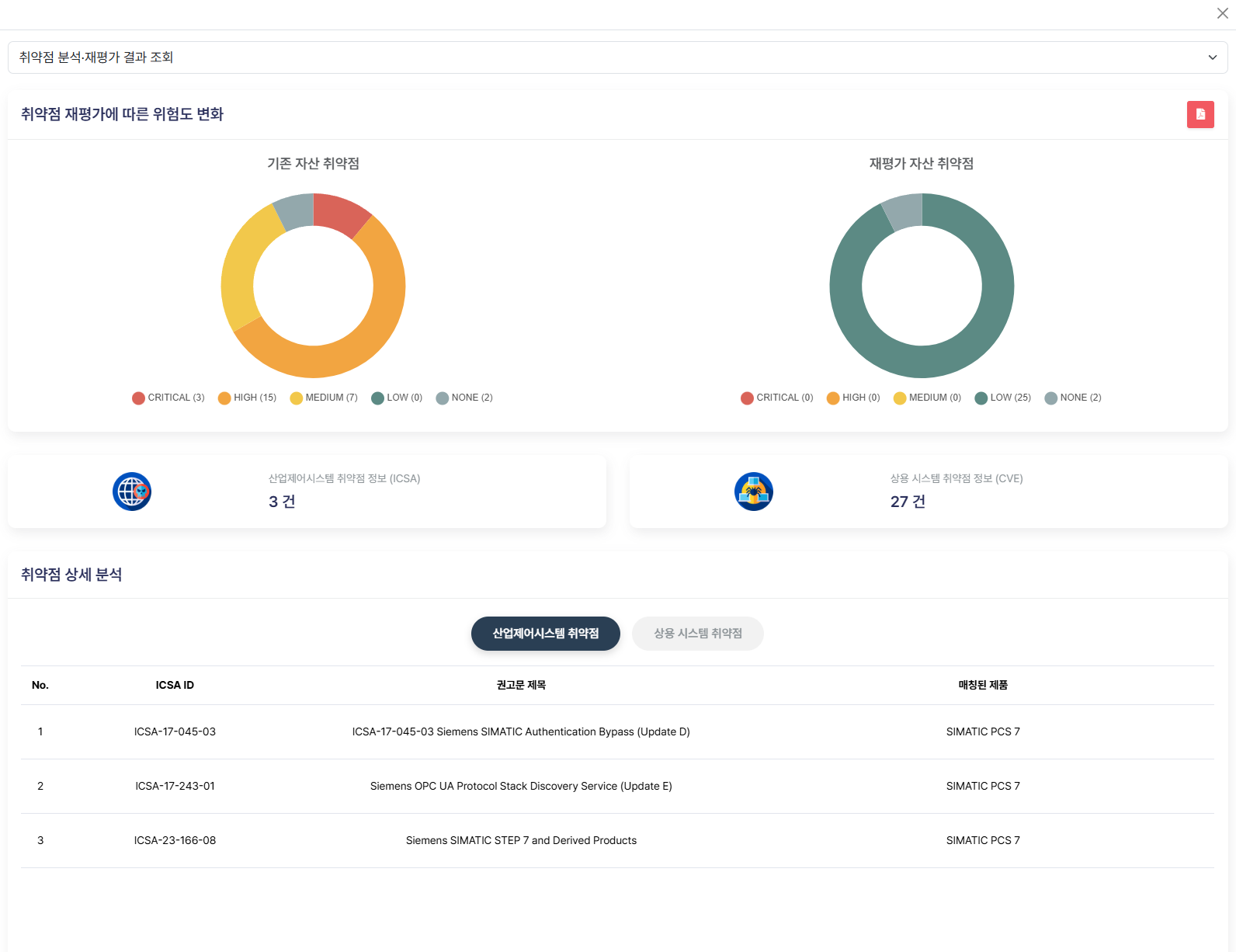
Vulnerability Analysis & Reassessment Results
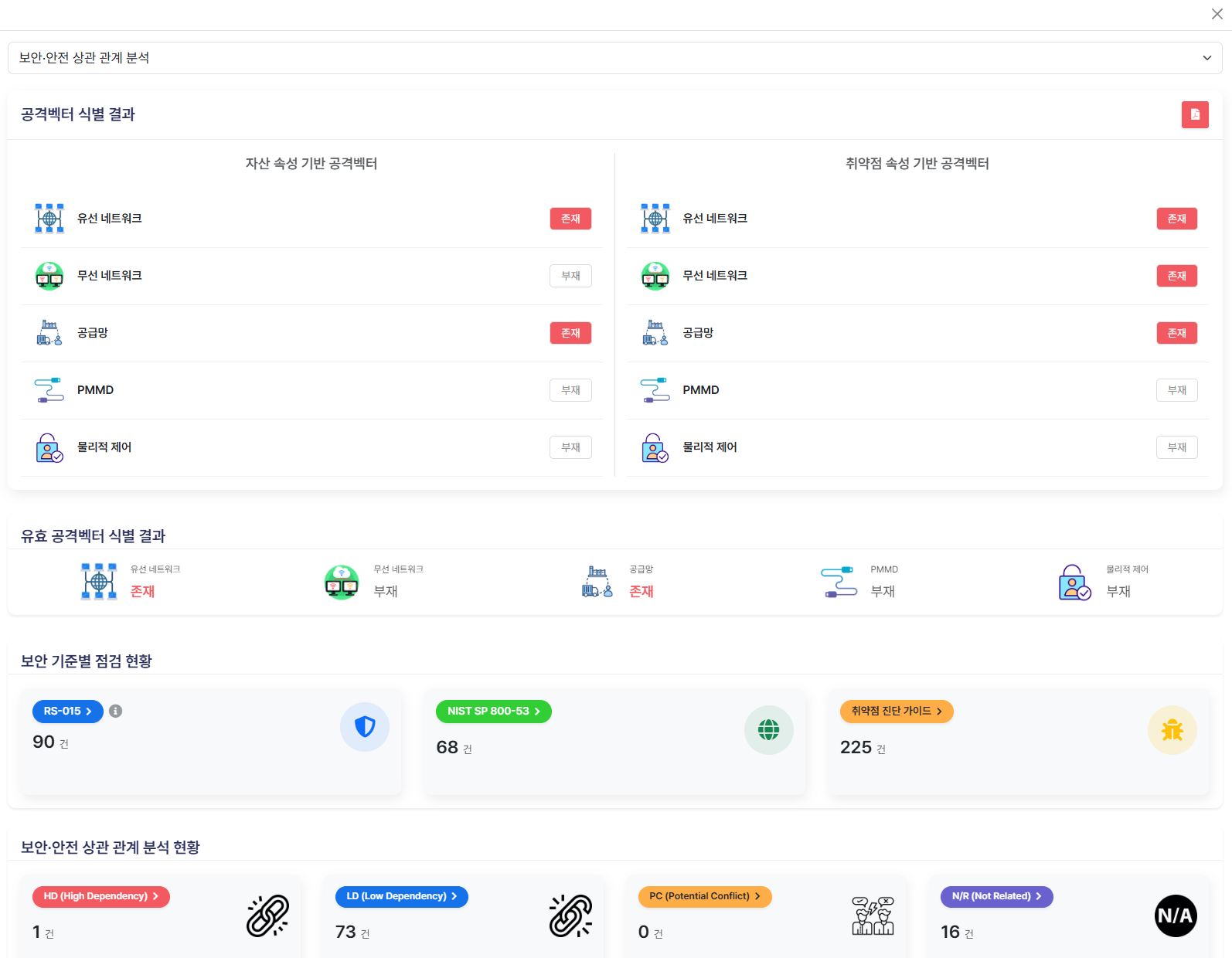
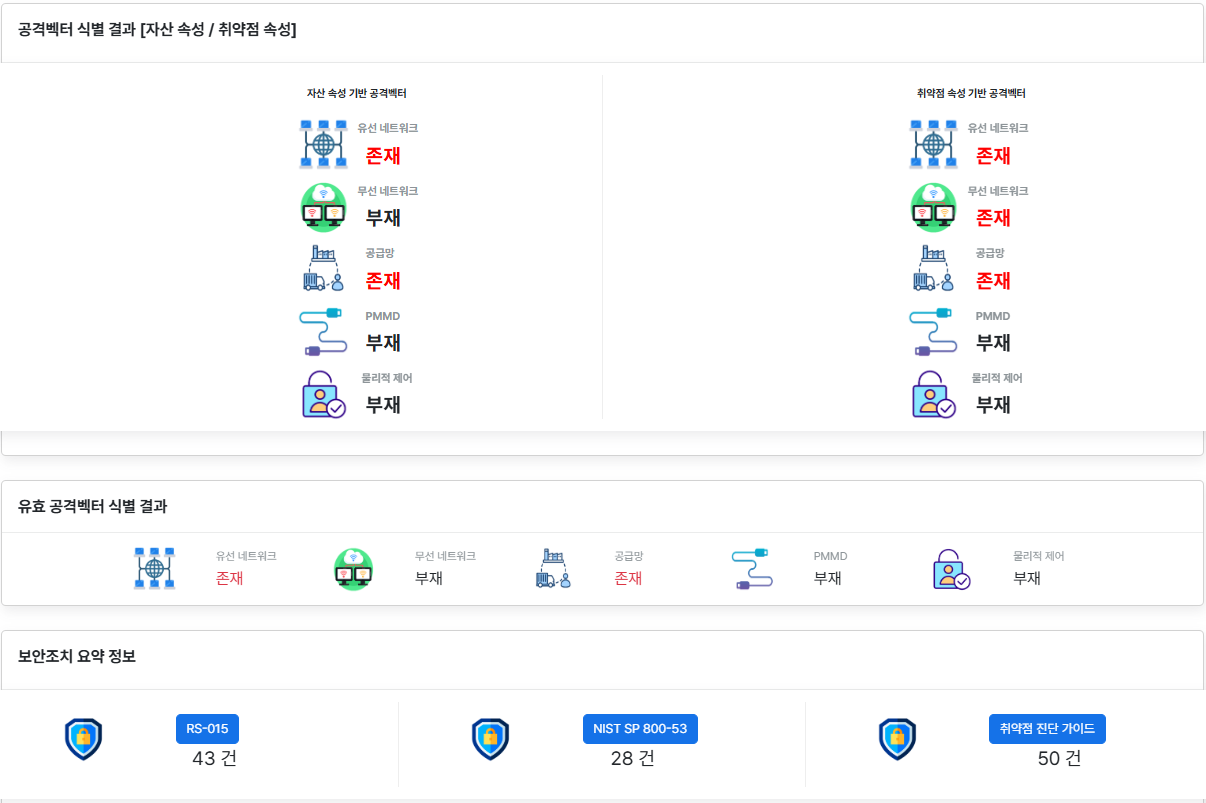
Step 05
Security & Safety Correlation Analysis